The dark web comprises roughly 6% of the internet as we know it. It is a gated or private cyberspace where all users are anonymous. Cybercriminals, drug dealers and hackers use it as a haven for malicious activities. But how does the dark web work, and what should you know to keep yourself and your business safe?
Chances are, you’ll never need to use the dark web. That doesn’t mean you shouldn’t protect yourself against those who do. We’ll explain how it works and why it breeds so many criminals. To get detailed answers to your questions, reach out to us at Thriveon. We proactively keep businesses safe from cyberattacks to prevent their assets from becoming commodities on the dark web.
How the Dark Web is Different
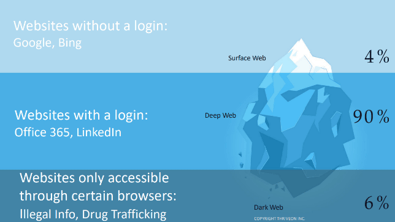
There are three layers to the World Wide Web:
- Surface Web (4%) – Any website that can be crawled that doesn’t require any type of login.
 Examples include Google, Yahoo, CNN and essentially any result you find during an internet search.
Examples include Google, Yahoo, CNN and essentially any result you find during an internet search. - Deep Web (90%) – The largest section of the web contains private information such as medical records, financial information, social media profiles and anything else that would require you to have a PIN or log in to access.
- Dark Web (6%) – It is only accessible through special browsers and decryption. It's often used to hide and sell sensitive information.
While the deep web and the dark web are similar, they serve different functions. The main difference between the dark web and the deep web is that the deep web is used to protect sensitive and personal information, while the dark web is used to exploit and monetize it illegally.
View recording: The Business Leader's Guide to Cybersecurity for the Modern Workplace
How Do People Access the Dark Web?
Anyone can access the dark web. It’s not an exclusive club or invitation-only cult. But a special browser is needed; Google, Safari and Bing aren’t going to cut it.
To enter the dark web, a TOR browser is needed. TOR is short for “The Onion Routing" Project, and all URLs on the dark web end in “.onion.” A TOR browser uses a three-layer proxy server that bounces the signal through multiple random and untraceable nodes posted by volunteers. The browser enters at a random node, is bounced through a randomly selected middle relay and then exits through a third node.
The effect of traveling through this random proxy system is that the user’s IP address, activity and history are all untraceable. They remain completely anonymous, as does everyone else using the dark web.
Is the Dark Web Illegal?
The dark web itself isn’t illegal, nor is using it. In some cases, the dark web even has positive benefits. In countries with oppressive regimes, activists and journalists can use it to spread their message and communicate with the outside world.
However, much of the other activity that takes place on the dark web is highly illegal. It’s estimated that 60% of the information on the dark web could harm individuals or organizations. Credit card numbers, bank account info, PayPal logins and much more can be bought and sold on the dark web. Criminals steal and sell information that could compromise an organization or business. Crime on the dark web continues to grow and has become a highly organized and extremely profitable enterprise.
Criminals use dark web markets to sell drugs, guns and other illegal contraband. Roughly 2-5% of the global gross domestic product (GDP) is laundered on the dark web annually. Criminals can set up an operation anonymously and disappear quickly, often leaving their paying clients out in the cold. There is little accountability for the activities that happen there.
Because it’s nearly impossible to track activity on the dark web, law enforcement agencies are limited in their ability to shut it down. The dark web isn’t limited to rogue hackers either. Organized crime organizations use it to extort billions of dollars. Unfortunately, bitcoin has only made it easier to conduct untraceable transactions.
How to Protect Your Business
The bad news is the dark web isn’t going away. Emboldened cybercriminals and bad actors will continue to use your data as a commodity – if they can get it. Keep your networks secure and your firewalls fortified with a comprehensive cybersecurity plan that anticipates attacks before they happen.
If you’re unsure where to start or if you’re looking for a third party to actively and constructively police your data and manage your security, schedule a meeting today. Our IT team specializes in helping Minnesota businesses like yours keep their assets off the dark web.


