Understanding and implementing cybersecurity best practices empowers you to protect your company against cyber attacks, which is a necessity in today’s digital age, especially for small and medium-sized businesses. If you know how solid or vulnerable your business is or where to make improvements, you can protect your data, networks and systems.
Your goal is to stay ahead of cyber attacks and the cyber criminals behind these attacks. A proactive approach and constant awareness are the best ways to mitigate cyber attacks, and having the best practices in place is the first step toward safeguarding your company.
Read: Cybersecurity Guidelines for Secure Behavior eBook
 Secure Your Networks with VPNs and Firewalls
Secure Your Networks with VPNs and Firewalls
Almost every business has Wi-Fi, and it’s essential to keep it secure. Keep your Wi-Fi hidden by setting up a wireless access point or router and then password-protecting it. Never use public Wi-Fi, especially for sensitive information. When you use public Wi-Fi, you share it with everyone connected, making your information vulnerable. If you have to use it, use Virtual Private Networks (VPNs), as they encrypt the traffic between the service and device to help protect information. Make sure your business Wi-Fi is separate from your customer Wi-Fi.
Firewalls can also help block threats and suspicious traffic, acting like a gatekeeper between your computer and the internet. Ensure all devices accessing the internet go through your router and firewall to avoid unauthorized access.
Control Access
This step is two-fold: you can control physical access and data access.
For physical access, you want to limit unauthorized users from physically accessing computers or other devices. Laptops and phones should be locked up when unattended. Keep a record of equipment and who has what, especially for remote employees. Implement a security system, like cameras and alarms. If you’re disposing of devices, reset them to their factory settings and wipe the hard drive. Delete sensitive data from CDs, flash drives and other equipment before destroying them.
For data access, you want to monitor user permissions and limit employee access only to the information they need for their jobs. Only a select number of trusted staff should have administrative rights. If an employee wants to install software, they need permission first. Ensure each employee has their own account so they aren’t sharing credentials. You should also implement multi-factor authentication, which is when employees must verify their identity before accessing company networks, data and web portals. All these steps help reduce potential exposure and unauthorized access to valuable information.
If an employee leaves your company, delete their passwords and accounts so they can’t access data. Collect any company badges or keys. You don’t want the chance of an inside threat to happen.
 Utilize Antivirus Software and Keep It Updated
Utilize Antivirus Software and Keep It Updated
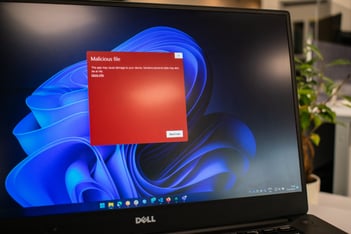
Antivirus, antimalware and antispyware software are excellent tools for deterring cyber attacks. Ensure every business computer, mobile phone or tablet has high-quality software. Spam filters and ad blockers also help.
More importantly, you need to keep these programs up to date to ensure the latest protection. Updates fix security holes and bugs, add new features and improve functionality, as outdated or vulnerable software is an easy way for hackers to get in. Never ignore updates; as soon as they’re available, install them. If you don’t have the time to update all your devices, turn on automatic updates.
This mindset should also apply to web browsers, applications and operating systems so that your entire infrastructure is secure.
Encrypt Data, and Back It Up
If you really want to deter hackers, encrypt data. Encryption converts data into a secret code, and the only way to access it is with an encryption key, so keep the key safe.
You should also regularly back up data, including word processing documents, electronic spreadsheets, financial files, human resources files and accounts receivable/payable files. If a breach occurs, you’ll have copies of data to minimize damages and prevent downtown and financial loss.
Follow the 3-2-1 rule with backing up data: Have three copies of files on two different media types and another copy off-site, like on cloud storage or an encrypted storage device. Back up data at least once a week, and test to ensure you can restore data from your backup.
 Have Strong Passwords
Have Strong Passwords
Hackers use password-cracking technology that tests thousands of potential passwords, so having strong, complex and varied passwords can make a world of difference. Here are some rules for creating strong passwords:
- Avoid common passwords like “password” or “123456”
- Make your passwords at least 19 characters long – long passwords are difficult to guess
- Your password should be a variety of letters, numbers and symbols, including uppercase and lowercase letters
- Don’t include easily guessable personal information in your password, like your birthday or pet’s name
- Use misspelled words in your passwords – these are exponentially harder to crack
- Leverage a password tester like passwordmonster.com to see how long it would take a hacker to crack your code
Don’t reuse passwords for multiple accounts, especially for business and personal accounts. If a hacker gets control of your password, they can try it on different websites or apps. You should also change them regularly (every 90 days) to thwart hackers.
For those who struggle to remember or create passwords, use a password manager to generate and store them. Don’t write down your passwords, and never share your password with anyone. If possible, set up account lockouts after a number of invalid password attempts.
Create a Strong, Effective Set of Guidelines and Policies
Your guidelines and policies should be multifaceted to improve cybersecurity and protect your company:
- Outline staff responsibilities and roles so they know exactly what to do when a cyber attack happens. This helps avoid misinterpretations and human error. You should also describe the consequences of data mishandling to discourage insider threats.
- Perform regular security audits to uncover vulnerabilities, gaps or suspicious activities and assess your security posture. You can then make the necessary improvements in case of a future breach.
- Include an incident response plan focusing on responding and recovering quickly from cyber attacks. Try to contain breaches so hackers can’t access other systems or data. You want to restore devices and data so your business can return to its normal operations.
- Know how to report the cyber attack to the authorities, customers, insurance providers or stakeholders in the event of a breach. Communicate recovery efforts, systems statuses and associated timelines.
Once you develop your guidelines and policies, you can then…
 Train Your Employees
Train Your Employees
One of the most common ways for cyber criminals to access sensitive data is through employees, especially if they’re working remotely. Your staff is your first and last line of defense against cyber attacks – all it takes for a cyber attack to occur is one ill-trained employee. If your employees don’t understand how to treat your business information and keep valuable data safe, you won’t have a chance against cyber criminals.
Train your employees about your company’s security practices so they can handle cyber threats and take the appropriate actions if something happens. If anything, they should know how to identify, report and avoid cyber attacks so your business stays secure.
Ideas like “Never Trust, Always Verify” and “Think Before You Click” are simple yet effective tools for employees – they should always think twice before clicking on an email or downloading an attachment, especially if they don’t recognize it or the sender. Verify links before you click on them, if you can, and never send out sensitive information to unknown persons. If a request seems off, it probably is, and it’s always better to double-check with the person in question before responding with information. Trust your gut.
Ongoing training and monthly newsletters are great ways to inform employees about cyber attacks. Share new types of cyber threats or how to prevent them from happening. Empower your staff so they feel like they can handle data breaches and threats with ease.
Need Help with Fighting Cyber Attacks?
Securing your future in the modern workplace will take more than the same old reactive IT support. If your business struggles with cybersecurity, has a limited budget or doesn’t have the time and resources to fight cyber crimes, don’t worry – outsourcing cybersecurity to skilled managed services providers (MSPs) like Thriveon is a great way to keep tabs on your network and data. Our fractional CIOs align you with best practices and strategically guide your technology spend to eliminate issues before they occur.
Schedule a meeting now to find out how we can help your company stay safe.

